Microsoft Intune is a cloud-based endpoint management solution that allows organizations to securely manage and enroll Android and iOS devices. Enrollment in Intune ensures that corporate policies, security settings, and app configurations are applied to mobile devices while maintaining user productivity.
For Android, iOS Devices Intune support enrolling Personal and Corporate devices with various Enrollment Methods (Apple DEP, Android Personal Owned Work Profile, Corporate Owned.. etc.).
Intune admins may wonder why a certain device model is enrolled or why devices are enrolling despite restrictions on that enrollment type. In this article from IntuneBytes, we’ll explain how to gain full control over iOS and Android enrollments.
Table of Contents
Android
Android mobile devices and tablets can be enrolled using Android Enterprise:
- Personal Owned Work Profile
- Corporate Fully Managed (COBO)
- Corporate Dedicated (COSU)
- Corporate Owned work Profile (COPE)
Android (VR Headsets and Teams Phones) can be enrolled using Android Open Source Project:
- Corporate User Associated
- Corporate Userless
Android Enterprise
Android Enrollment Restriction
The Personally Owned Work Profile is the only Android Enterprise enrollment type that can be managed through android enrollment restrictions. With this restriction, you can control enrolled device models, Android versions, and whether devices are personal or corporate-owned.
How to setup Android Enrollment Restriction
From Intune Admin Center > Devices > Android > Enrollment > Device Platform Restriction > Android Restriction and create new

Explanation per numbers in snapshot:
1- Platform: If enabled, Android Enterprise Personal Work-Profile Enrollment is allowed. If disabled, enrollment is not allowed tenant-wide level.
2- Versions: minimum and maximum android versions allowed for enrollment. This is very helpful top block Beta Versions.
3- Personally Owned: If enabled, enrollment will be allowed for all devices. If disabled, only Corporate Device Identifiers are allowed for this enrollment
4- Device Manufacturer: If any Manufacturer is added there, then it’ll be blocked.
Finally, Android Enrollment Restriction MUST be assigned to User Group ONLY.
Corporate Device Identifiers
Corporate device identifiers for Android are currently not functional due to Google’s restrictions on sharing device serial numbers during enrollment with any MDM providers, citing privacy concerns. As a result, starting from Android 12 and later versions, the use of corporate device identifiers in Intune or any other MDM solution is no longer supported.”
Corporate Enrollment
1- Corporate Enrollment includes (Android Enterprise Fully Managed, Dedicated and Corporate Devices with Work-Profile).
2- Android Enrollment Restrictions are not effective on Corporate Enrollment.

3- Corporate enrollment typically involves using a QR code or an enrollment token, giving administrators full control over whether to share these with users.
The most secure approach is to leverage Samsung Knox enrollment or Google Zero-Touch enrollment. These methods allow administrators to manage all Android devices from a single interface and assign the appropriate enrollment profile to each device, ensuring centralized control and enhanced security.
KNOX VS Google ZTE
- Android Google Zero touch cover all Android Certified Devices however Samsung Knox only controls Samsung Knox devices.
- Google Zero touch Admin Center can be linked in Intune Admin Portal to have centralized Management in one Portal.
- Samsung KNOX provides more features within KNOX Suite (Force OS Updates, OEM-Profile… etc.)
How Samsung KNOX or Google ZTE works
1- Intune admin must create an enrollment profile based on type of enrollment needed.
From Intune Admin Center > Devices > Android > Enrollment > (for example) Corporate Owned Fully Managed> create profile.. give it name, Token type and then create.

2- Open the created profile and select Token and copy enrollment Token.

3- In KNOX Admin Portal or Google Zero Touch Enrollment Portal, you’ve to create an enrollment profile and edit JSON file to contain the same token from your Tenant.
4- When a Samsung device boots up and connects to Wi-Fi, it communicates with Knox servers to check whether it is associated with a corporate organization. Similarly, with Google Zero Touch, the device connects to Google ZTE servers to determine whether it is a personal or corporate-owned device.
5- If the Device is added to Samsung KNOX or Google Zero Touch and assigned to enrollment profile with (JSON and Tenant’s Token included), JSON file is sent from Samsung KNOX or Google Zero Touch Servers to the device Directly to start Enrollment.
AOSP Enrollment
- AOSP Enrollment Types are all Corporate, Android Enrollment Restrictions are not effective.
- Can’t be enrolled with Google Zero Touch.
- VR/AR Headsets need to scan QR Codes
- Teams Devices (updated to AOSP Firmware) doesn’t need to Scan QR Enrollment Code.
Apple Devices (iOS and iPadOS)
iOS and iPadOS devices can be enrolled in Intune:
- Account-Driven User Enrollment
- Device Enrollment
- Web Based Device Enrollment
- Via Company Portal
- Via Apple Business Manager Or Apple School Manager
iOS Enrollment Restriction
iOS Enrollment Restriction have 2 options:
- Block/Allow MDM Enrollment.
- Block/Allow Personal Devices: If Blocked, all Personal Devices will not be allowed for enrollment until device is added in Corporate Device Identifier List (to be recognized as Corporate Device).
What to Consider when Planning iOS Enrollment Restriction
1- iOS Enrollment restrictions are applied to any user-affinity enrollment in Intune for Apple devices which includes corporate and personal enrollment.
2- If iOS Enrollment Restriction is disabling MDM Platform, Personal or Corporate Enrollment will fail. Below is example of error message for Setup Assistant with Modern Authentication enrollment failing due to MDM Platform is disabled.


3- Userless Apple Business/School Manager Enrollment will apply Default iOS Enrollment Restriction. MDM Platform MUST be Allowed.
4- OS Version in iOS Enrollment Restriction is only Applicable for Enrollments initiated via Company Portal Application.
Need to Allow only Corporate Devices
If your Organization requires enrolling only Corporate Devices, please follow below actions:
- Default and New iOS Enrollment Restrictions MUST have MDM Allowed.
- Personally Owned Devices should be blocked.
- Any Device MUST be added in Corporate Device Identifier List (either Serial Number or IMEI Number).
iOS Enrollment Restrictions added via Intune Portal > Devices > iOS > Enrollment > Device Platform Restrictions

Corporate Identifier can be created through Intune Portal > Devices > Enrollment > Corporate Device Identifiers and then add

How ABM/ASM Enrollment Works
1- Corporate Devices MUST be added to Apple Business or School Manager (either manually or automatically via Apple or Reseller).
2- Device Should be added to Correct MDM-Server (Which is Apple DEP Token added to your tenant).
From ABM > Devices > Search with Device SN > and ensure MDM Server (DEP Token) in your Tenant

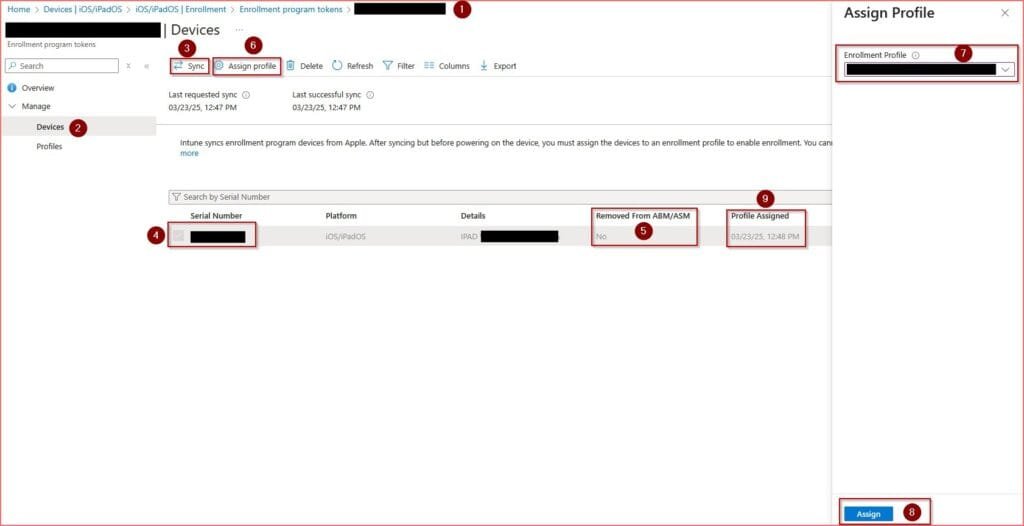
3- Sync DEP Devices from Intune Tenant via Intune Portal > Devices > iOS > Enrollment > Enrollment Program Token > select DEP Token then sync
4- Ensure that device is manually or automatically assigned DEP Enrollment Profile.
5- When device is wiped and go through Setup Assistant, it’ll communicate with Apple for Device Activation. Then device will retrieve Enrollment Profile from Assigned Tenant.




Leave a Reply